The Architecture of Amnesia: Why Enterprise Security Requires a Memory
Modern cybersecurity is trapped in the present tense. I explore the epistemological blind spot of real-time defense—and why I built TensorGuard to fix it.

A modern operating system is a machine purpose-built to forget.
Beneath the sleek graphical interfaces and the illusion of permanence, the Windows kernel is a fiercely dynamic environment that constantly cannibalizes its own history. To optimize performance and preserve disk space, it relentlessly overwrites cache files, vacuums SQLite databases, and reallocates memory space. It is a system that exists almost entirely in the present tense.
For the past decade, the cybersecurity industry has mirrored this architectural amnesia. We have poured billions of dollars into fortifying the perimeter. We have constructed vast digital panopticons governed by Endpoint Detection and Response (EDR) platforms. These systems—marvels of modern software engineering—stand guard over the operating system, deeply hooking into active memory to monitor system calls and terminate malicious execution the exact millisecond a behavioral heuristic is triggered. They are the undisputed sentinels of live defense. They are designed to catch the bullet in mid-air.
When they succeed, it is spectacular.
But relying exclusively on EDR for enterprise visibility introduces a profound epistemological flaw. An EDR agent operates identically to a live security camera. It is exceptionally capable of stopping a break-in currently in progress, but it possesses a catastrophic blind spot: a live camera cannot see what successfully evades its lens, nor can it remember what occurred in the hallways before it was installed.
This is the "live-feed fallacy" of modern cybersecurity. We have equated a silent, green dashboard with the absolute absence of a threat. But silence is not security. Nor is starting every day with the baseline assumption of "we're fine." Silence is simply the absence of an alarm.
The Ruins of the Present Tense
Before I began building security architecture, I spent my days analyzing its failures. While securing launch control infrastructure at NASA, and later during my tenure as an incident responder at Palo Alto Networks' Unit 42, I was routinely parachuted into the smoldering digital ruins of compromised enterprises. I tracked state-sponsored adversaries, unraveled sophisticated ransomware deployments, and investigated catastrophic insider data exfiltrations.
What became immediately apparent in the trenches was that modern adversaries rarely kick down the front door. They do not drop noisy, easily signatured malware payloads onto a disk where an EDR can simply block them. Instead, they log in.
Through Adversary-in-the-Middle (AiTM) phishing frameworks that seamlessly steal session cookies, or by purchasing compromised credentials on the dark web, attackers hijack legitimate, highly privileged administrative tools. They "live off the land," utilizing native Windows binaries like PowerShell, Windows Management Instrumentation (WMI), or certutil.exe. Because these tools are cryptographically signed and legitimately required for daily corporate IT operations, real-time sensors are fundamentally hesitant to block them outright. If an EDR aggressively terminates a legitimate administrative process, it risks bringing down a critical production server.
So, the sensor hesitates. The adversary blends into the background noise of the enterprise. They evade the live feed.
When the silence finally breaks—usually heralded by a ransom note or an extortion email containing stolen intellectual property—the autopsy begins.
When the perimeter falls and the live sensors are bypassed, the only remaining source of truth is the endpoint itself. While the live memory of a computer is ephemeral, the hard disk is an obsessive, compulsive diarist. Every action a user takes leaves a microscopic fracture in the digital bedrock.
The deep, immutable ledgers of the operating system—the Master File Table ($MFT), the AmCache, the System Resource Usage Monitor (SRUM), and the ShellBags—hold the undeniable ground truth. They tell you exactly when a portable extraction tool was executed from a USB drive, or which specific application beaconed to a foreign IP address three weeks ago.
The evidence is always there. The problem is the arithmetic of the autopsy.
The Economics of Artisanal Forensics
Studying the intersection of computer science and economics at Yale University, we were taught to become obsessed with systemic market inefficiencies. The traditional Digital Forensics and Incident Response (DFIR) industry was a glaring one.
Digital forensics is an incredibly deep, evidence-based science. But historically, it has been treated as an artisanal craft—an autopsy performed with a trowel while the building is actively burning. Extracting registry hives, parsing hexadecimal data into massive, readable CSV spreadsheets, and manually correlating UTC timestamps across thousands of endpoints takes elite investigators hundreds of hours.
Analyzing a single endpoint manually takes a senior examiner several hours. If a Fortune 500 company suspects a fleet-wide compromise across thousands of servers, or some unknown selection of them, manual human triage becomes mathematically impossible. You cannot throw enough human labor at the problem. It would take a team of analysts weeks or months to establish an initial baseline.
This creates a massive economic vulnerability. In cybersecurity, time is not just money; time is an exponential liability. The longer a threat actor dwells undetected within a network, the more catastrophic the financial and reputational damage becomes. We were attempting to solve an industrial-scale data problem with bespoke, hourly-billed human labor.
My senior thesis at Yale—for which I was honored to receive the Herbert Scarf Award—focused heavily on this intersection of computational mechanics and economic constraints. The fundamental question was clear: How do we collapse the cost of certainty? How do we transition digital forensics from a reactive, unpredictable cost center into a proactive, continuous capability?
We needed a fundamental paradigm shift. We did not need more real-time sensors generating more stochastic, ambiguous alerts. We needed to democratize the ground truth. We needed to operationalize digital forensics.
Teaching the Network to Remember
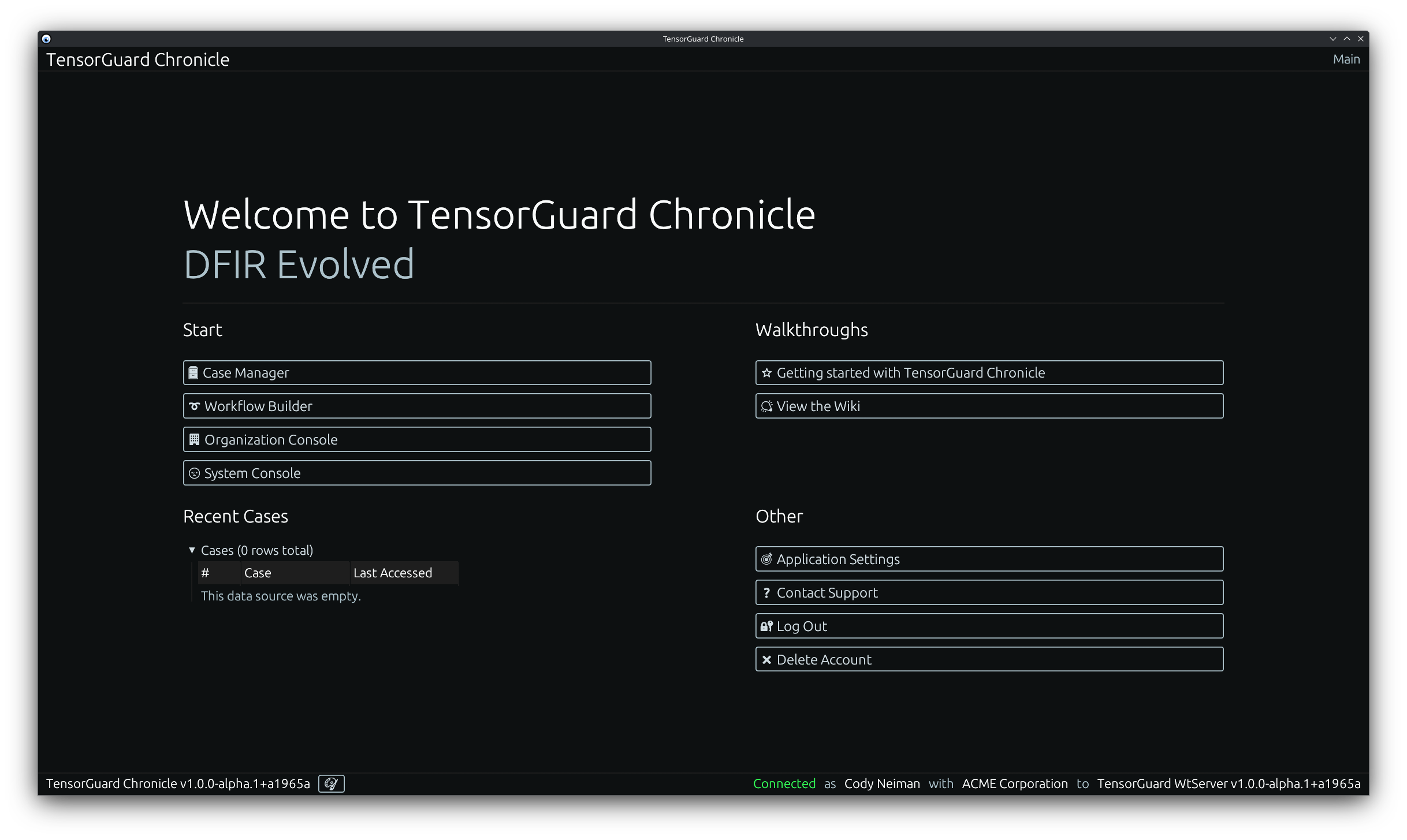
This cognitive dissonance—the gap between the theoretical necessity of historical evidence and the logistical impossibility of acquiring it at scale—was the genesis of TensorGuard.
I founded TensorGuard on a singular, uncompromising thesis: we must give the endpoint a memory. We had to transform the retroactive, catastrophic cost center of incident response into a proactive, automated software capability.
To do this, we had to fundamentally rearchitect the forensic lifecycle. We completely decoupled the act of data collection from the act of analysis. Through a lightweight, read-only collector, TensorGuard allows organizations to instantly freeze an endpoint's deep historical artifacts in cryptographic amber. By compiling an immutable, FIPS-aligned .spade package in minutes, we capture the history before the operating system can overwrite it, and before the adversary can wipe it.
Collect now, analyze later.
But collecting the data is only half the battle; the true friction lies in the interpretation. Dropping millions of rows of CSV data onto an overwhelmed Tier 1 SOC analyst does not solve the talent shortage; it exacerbates it.
To solve the human bottleneck, we built the TensorGuard Evie Intelligence Engine. By fusing the rigorous, time-tested statistical methods of digital forensics with advanced, large-scale artificial intelligence, TensorGuard processes billions of rows of raw binary and registry data in parallel. What previously took a team of forensic consultants weeks to manually correlate is now synthesized into a C-Suite ready executive summary and an interactive timeline in under ten minutes.
Crucially, we reject the "black box" nature of modern AI hype. Every single behavioral anomaly and timeline event generated by TensorGuard is directly cited and hyperlinked to the underlying raw disk data. We do not ask security teams to blindly trust an algorithm; we provide the cryptographically sound proof required for absolute legal defensibility in high-stakes legal proceedings, HR investigations, or Mergers & Acquisitions (M&A) due diligence.
The End of the Blind Spot
By operationalizing digital forensics, we change the entire posture of the Security Operations Center.
Instead of waiting for an EDR sensor to flash red, analysts and internal threat hunters can now proactively interrogate their fleet using plain human language. They can ask, "Has the credential-dumping tool mimikatz.exe ever been run on these domain controllers?" or "Show me all devices where a USB drive was connected in the last 72 hours, and exactly what files were accessed."
They receive an evidence-backed answer in minutes. We transition the enterprise from a state of anxious, reactive firefighting to a state of continuous, proactive validation.
When you remove the friction of human labor from digital forensics, you unlock entirely new operational paradigms. Corporate Development teams no longer have to rely on brittle security questionnaires during M&A due diligence; they can run a TensorGuard Enterprise Sweep to definitively prove a target company's network isn't harboring a dormant APT before the acquisition closes. Human Resources teams investigating intellectual property theft no longer have to wait weeks for external validation; they can generate airtight, legally defensible timelines of data exfiltration in the same afternoon.
Security is, at its core, an ongoing war against information asymmetry. For too long, we have allowed adversaries to operate comfortably in the blind spots of our live-monitoring tools, banking on the fact that digging into the past was too expensive for defenders to justify.
The cybersecurity industry has spent the last twenty years chasing the speed of the present. But as adversaries grow increasingly adept at slipping past our live cameras, it's no longer an acceptable substitute.
The future of enterprise defense will not be won by simply building faster sensors.
It will be won by those who can rapidly, affordably, and accurately interrogate the past.
Truth, in the digital age, requires a memory. It is time we engineered our defenses to remember.
